Every engineer knows that a single point of failure is a design flaw. It’s the first rule of system architecture, yet the European Union is built entirely on it. You have a massive, complex network of 32 nodes, and just one corrupted input can halt the entire process. It’s not just a diplomatic headache; it’s a fundamental logic error in the code that’s currently being exploited by players who understand the mechanics better than the architects.
Under the Hood
The Man-in-the-Middle Attack Viktor Orban is operating like a compromised admin account inside the EU network. He’s technically part of the system, but his primary loyalty lies with an external server (Russia). By utilizing his veto power, he introduces latency and errors into any packet of data meant to sanction Moscow. It’s a classic denial-of-service attack, but executed through official channels.
Cross-Scripting the Election It’s not just Hungary; the Slovakia node is getting involved too. Robert Fico is essentially threatening to block Ukraine aid packages if the Hungarian “patch” (the election) doesn’t go the way the Kremlin wants. This looks less like diplomacy and more like a botnet coordinating a synchronized strike to keep a compromised leader in power.
Social Engineering at Scale

You aren’t just fighting politics; you’re fighting algorithms. There are reports of GRU squads in Budapest running the same playbooks they used in Moldova—flooding the network with AI-generated TikTok content and fake engagement metrics. They’re farming “likes” to simulate consensus, trying to trick the user base into thinking the malware is actually a popular feature.
- Legacy Code is Killing Performance
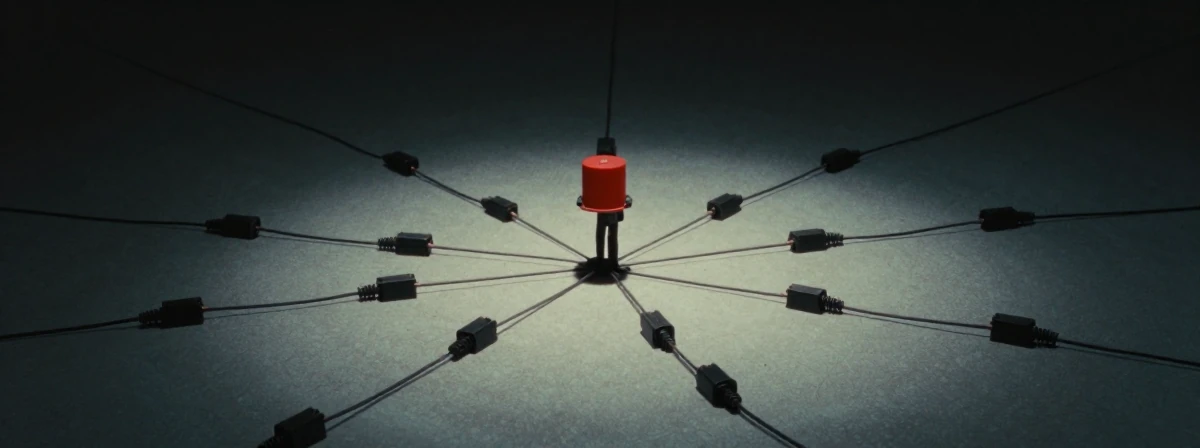
The requirement for unanimous voting is technical debt that the EU refuses to refactor. It might have worked when the user base was small—maybe France, Germany, and the UK—but scaling that architecture to 32 members is a disaster waiting to happen. When you give every single user a “kill switch” for the entire platform, you don’t get cooperation; you get hostage situations. The system is optimized for gridlock, not throughput.
- Bandwidth isn’t free You can’t throttle updates for other nodes and then act surprised when the central server cuts off your funding. It’s simple logic: if you degrade the network service, you don’t get the premium package.
We’re watching a live stress test of a system that was never designed to handle malicious internal actors. You can patch the bugs with elections, but until the developers address the fundamental flaw in the permission settings, the exploit will remain. The only way to secure the network is to remove the kill switch from the bad actors.
